Some Apple users are reportedly being targeted by a sophisticated attack, requesting them to hand over their Apple ID credentials over and over again.
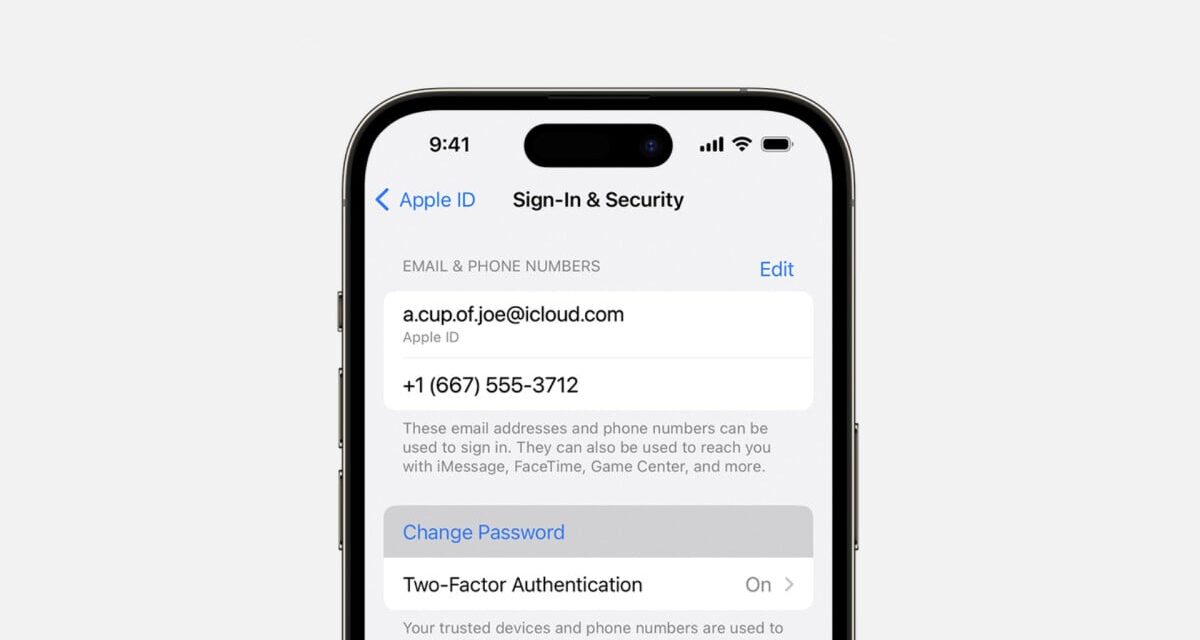
According to KrebsonSecurity, the attack starts with unsuspecting Apple device owners getting dozens of system-level messages, prompting them to reset their Apple ID password. If that fails, a person pretending to be an Apple employee will call the victim and try to convince them into handing over their password.
This is exactly what happened to entrepreneur Parth Patel, who described their experience on Twitter/X. First, all of Patel’s Apple devices, including their iPhone, Watch, and MacBook, started displaying the “Reset Password” notifications. After Patel clicked “Don’t Allow” to more than one hundred requests, the fake Apple Support called, spoofing the caller ID of Apple’s official Apple Support line. The fraudster Apple employee actually knew a lot of Patel’s real data, including email, address, and phone number, but they got their name wrong, which had confirmed Patel’s suspicions that they were under attack.
While the attack was ultimately unsuccessful in this example, it’s easy to imagine it working. The victim might accidentally allow the password reset (mistakes are easy to happen when you have to click on something hundreds of times), or they could fall for the fairly convincing, fake Apple Support call.
Patel’s example isn’t isolated, either; KrebsonSecurity özgü details on a very similar attack that happened to a crypto hedge fund owner identified by his first name, Chris, as well as a security researcher identified as Ken. In Chris’ example, the attack persisted for several days, and also ended with a fake Apple Support call.
How did the attackers know all the data needed to perform the attack, and how did they manage to send system-level alerts to the victims’ phones? According to KrebsonSecurity, the hackers likely had to get a hold of the victim’s email address and phone number, associated with their Apple ID. Then they used an Apple ID password reset biçim, that requires an email or phone number, alongside a CAPTCHA, to send the system-level, password reset prompts. They also likely used a website called PeopleDataLabs to get information on both the victim and Apple employees they impersonated.
But there could also be a bug in Apple’s systems, which should in theory be designed not to allow someone to abuse the password reset biçim and send dozens of requests in a short period of time (Apple did not respond to KrebsonSecurity’s request for comment).
It appears that there’s no easy or foolproof way to protect oneself from such an attack at this time, save from changing one’s Apple ID credentials and tying them to a new number and email. It’s hard to tell how widespread this attack is, but Apple users should be vigilant and triple-check the authenticity of any password reset request, even if it appears to come from Apple itself.
For on spammers and scammers, check out Mashable’s series Scammed, where we help you navigate a connected world that’s out for your money, your information, or just your attention.
Topics
Apple
Cybersecurity